FDA releases draft guidance “Content of Premarket Submissions for Device Software Functions”
New Approach:
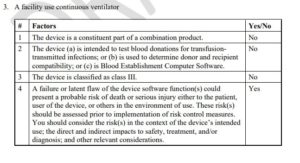
When Enhanced Level of documentation will be required?
1) The device is a constituent part of a combination product.
2) The device (a) is intended to test blood donations for transfusion-transmitted infections; or (b) is used to determine donor and recipient compatibility; or (c) is a Blood Establishment Computer Software.
3) The device is classified as Class III.
4) A failure or latent flaw of the device software function(s) could present a probable risk of death or serious injury, either to a patient, user of the device, or others in the environment of use. These risk(s) should be assessed prior to implementation of risk control measures. You should consider the risk(s) in the context of the device’s intended use; the direct and indirect impacts to safety, treatment, and/or diagnosis; and other relevant considerations.
FDA Example:
Outcome: The device is not a constituent part of a combination product, is not Blood Establishment Computer Software, and is not intended for use in testing blood donations for transfusion-transmitted infections or determining donor and recipient compatibility. The device is class II. However, a failure or latent flaw of the device software function(s) (e.g., exploited cybersecurity vulnerability compromises device functionality) would present a probable risk of death or serious injury to a patient (e.g., loss of life supporting function) prior to the implementation of risk control measures. Therefore, this device would fall under “Enhanced Documentation Level.”
Medtronic Receives a Warning Letter from the FDA
Excerpts:
Log4j is broadly used in a variety of consumer and enterprise services, websites, and applications—as well as medical devices and supporting systems—to log security and performance information. There is active, widespread exploitation of the vulnerability across various industries.
(This is remote code execution vulnerability (CVE-2021-44228) affecting Log4j versions 2.0-beta9 to 2.14.1. A remote attacker could exploit this vulnerability to take control of an affected system. Log4j is an open-source, Java-based logging utility widely used by enterprise applications and cloud services).
These vulnerabilities may introduce risks for certain medical devices where the device could be made unavailable, or an unauthorized user could remotely impact the safety and effectiveness of device functionality. At this time, the FDA is not aware of any confirmed adverse events affecting medical devices related to these vulnerabilities.
Manufacturers should assess whether they are affected by the vulnerability, evaluate the risk, and develop remediation actions. As Apache Log4j is broadly used across software, applications, and services, medical device manufacturers should also evaluate whether third-party software components or services used in or with their medical device may use the affected software and follow the above process to assess the device impact.
© 2025 BeanStock Ventures